
10 Insightful Web Security Tips for Safe Browsing
Author: Shekhar Pawar, CEO, GrassDew IT Solutions Private Limited
May 29, 2020
Websites are prone to hacking, defacement, cryptojacking, and various other forms of attacks. According to a Clark School study at the University of Maryland, there is a web attack every 39 seconds on average. This indicates the need for security professionals to consider web security as a critical element in keeping cyber attackers away from accessing sensitive data. Mostly, these attacks start with phishing, one of the social engineering attacks, which is then followed by malware, ransomware, credential stuffing, and other cyberattacks. There is an urgent need for the security team to provide proper security training and education to regular employees to mitigate social engineering threats.which is then followed by malware, ransomware, credential stuffing, and other cyberattacks. There is an urgent need for the security team to provide proper security training and education to regular employees to mitigate social engineering threats.
What Is Web Security?
Cybercriminals use automated programs and tools to detect susceptible websites. They then launch an attack to exploit the identified flaws, trying to gain access to confidential data. Web security involves various methods, tools, and participation from the security professionals in keeping perpetrators away from the websites by identifying and patching up the vulnerabilities.
Why Is Web Security Needed?
Web security protects businesses from financial loss and preserves reputational value and unwanted shutting down of the website. A web attack can lead to a website crash or slow response, severely impacting the business. With proper web security strategy, security professionals can help the business grow without interruption or loss due to compromised information security.
Here are some useful tips to keep a website protected from attackers. Some of these step could also be carried out by the security/network admins of an organization or an ISP to protect their users.
1. Use a trustworthy web browser
Popular web browsers like Mozilla Firefox, Google Chrome, and Windows Internet Explorer/Edge provide regularly updated web security assistance that helps deal with malicious URLs. Try to keep your web browser on auto-update mode or update it periodically.
2. Web browser’s privacy and web security settings
You need to maintain the browser's privacy and web security settings to protect your identity and avoid a data breach. For example, you can include a "Do Not Track" request with your browsing traffic. You can also disable the web camera or microphone so that malicious applications and websites are unable to access it.
3. Beware of short URLs
Shortened URLs are one of the main methods that attackers use to hide and modify malicious URLs. When their targets receive a short URL and click on it, it is very difficult for them to know where it will navigate, as, unlike hyperlinks, short URLs may show the same link address even upon hovering your cursor over the link. Hence, it is hard to detect whether; it is a cyber trick and/or it will navigate to some fake website created for a phishing attack.
Short URLs are usually generated by converting regular URLs with the help of various applications involved with digital marketing. An example of a short URL is given below:
Actual long URL: https://www.socialpilot.co/blog/importance-url-shortener-social-media-marketing
Corresponding short URL: https://bit.ly/3wG0M90
Similarly, using different URL validators or URL unshorteners (many of which are available online), you can see the long URL for the short URL you received, hence helping you determine whether the URL is malicious or not. Some of the online opensource applications for this purpose are:

4. HTTPS is better than HTTP URL
You may have noticed that some website URLs start with HTTP while others have HTTPS, where the latter is actually HTTP with encryption, i.e., secured. HTTPS protocol has TLS (SSL certificate) to encrypt normal HTTP requests and responses; thus, enhancing web security over regular HTTP. Hence, it is advised only to visit sites and links that are encrypted, i.e., HTTPS.
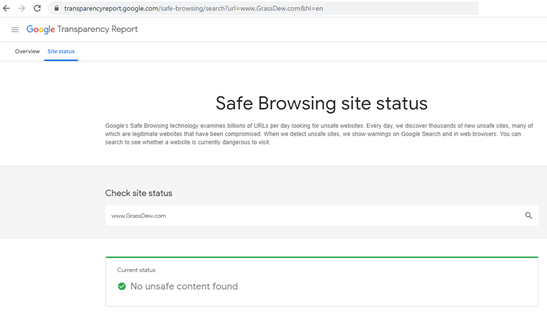
5. Check Google’s safe browsing site status.
As mentioned earlier, many browsers have various web security features, and one of the most popular is Google's Safe Browsing technology that examines billions of URLs per day and tries to detect unsafe websites. Every day, thousands of new unsafe sites are discovered by this method, many of which are legitimate websites that have been compromised. When they detect unsafe sites, they show warnings on Google Search and in web browsers. You can also search to see whether a website is currently dangerous to visit using the Googles transparency report application at https://transparencyreport.google.com/safe-browsing/search?hl=en
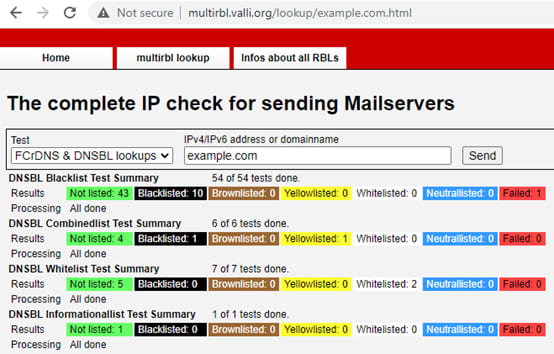
6. Check if the website IP itself is blacklisted
There also exist other online tools that help us check if the website IP Address is listed in the Global Blacklist Database. One such popular tool is Multiball, which is a free multiple DNS BlackList, aka RBL (DNSBL) lookup online tool. http://multirbl.valli.org/
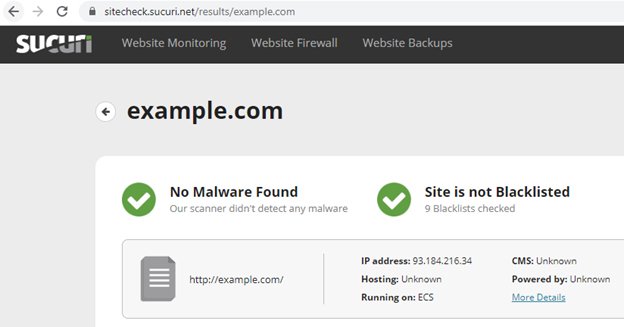
7. Check website reputation
Several online tools as service run the website through multiple blacklist engines and analyze its online reputation using different tools to facilitate the detection of fraudulent and malicious websites. It helps you easily identify websites involved in any malware or fraudulent activities. This process also helps in obtaining information if a particular site is whether a phishing website or not. Some of the popular online tools are listed below:
- Norton safe web (https://safeweb.norton.com/)
- TrendMicro Site safety (https://global.sitesafety.trendmicro.com/index.php)
- mxtoolbox (https://mxtoolbox.com/)
- urlvoid (https://www.urlvoid.com/)
8. Know the source of the website URL
Different website scanners help check a website for any known malware, blacklisting status, viruses, website errors, out-of-date software, and malicious code. There are quite a few website scanners that can help you to know more about any website.
- Web Inspector (https://webinspector.com/website-malware-scanner)
- Sucuri (https://sitecheck.sucuri.net)
- PCrisk (https://scanner.pcrisk.com)
9. Make it a habit to not directly click any unknown URL
Just for example, if you have received a URL, which is very familiar to you, copy-paste it in the browser – or – don't click and allow it to automatically open with the default browser of your device. Instead, it is better to type it in a web browser. It minimizes the risk of becoming a victim of cyber tricks.
10. Contribute to reporting malicious websites
You can report the dangerous URL to the few below-listed services. They will do more analysis of your reporting, and it will help many.
- Fortinet (https://www.fortinet.com/)
- Sophos (https://www.sophos.com/en-us.aspx)
- Trustwave (https://www.trustwave.com/en-us/)
- Bitdefender (https://www.bitdefender.com/solutions/trafficlight.html)
- Norton (https://safeweb.norton.com/)
- Stopbadware (https://www.stopbadware.org/clearinghouse/search/)
An effective web security strategy requires well-trained staff who understand how malicious hackers usually work. Thus, a simulated phishing campaign can empower the team to help understand how hackers can manipulate users to compromise sensitive information and mitigate it. Securing your employees from online scammers will reduce the chances of your corporate website falling for cyberattacks.
Some of the security issues can easily be resolved with the adoption of security awareness training. Security team enabled with a training program can keep a detailed report on the security chain’s weakest link and improve them. Also, they can then either limit access to these links or strengthen them against attacks.
FAQs
A. There is a need to protect any web or cloud that collects private information from the user or it becomes quite easy for attackers to steal it. Without web security, hackers can even hijack or crash the site.
Read more at: https://blog.eccouncil.org/why-is-web-security-important-for-enterprises/
A. SSL is an acronym for Secure Sockets Layer. It is a security protocol that offers authentication, privacy, and integrity to internet communications.
Read more at: https://blog.eccouncil.org/your-ssl-certificate-is-more-important-than-you-think/
A. Phishing attacks are one of the most common forms of security challenges at both individual and organizational levels. Under such attacks, cybercriminals try to gain unauthorized access to legit login credentials, credit card details, and other sensitive data.
Read more: https://blog.eccouncil.org/how-strong-is-your-anti-phishing-strategy/